USA Today
A Russian invasion could reach farther than Ukraine. How a cyberattack could affect you.
Josh Meyer and Kevin Johnson, USA TODAY – February 17, 2022
WASHINGTON – Russian President Vladimir Putin’s track record of unleashing destructive “hybrid warfare” cyberattacks has U.S. security officials fearing he could once again reach across continents and wreak havoc on unwitting Americans as worries about a possible Russian invasion of Ukraine persist.
They call it the “spillover effect.” And they say the temporary takedown of some prominent Ukrainian military and financial sector websites Tuesday resembled the kind of prelude to more significant Russian cyberwarfare attacks that could get out of hand.
Russia has a long and demonstrated history of unleashing such powerful cyberweapons against its adversaries, former top Pentagon cybersecurity official Lucian Niemeyer told USA TODAY.
And once that happens, they can spread virtually anywhere – and potentially everywhere – without the ability to control them he said.

“Anytime we see that cyber is involved in an attack around the world, there’s always the potential that it can spread quickly and have unintended consequences,” said Niemeyer, who served as Assistant Secretary of Defense for Energy, Installations and Environment from 2017 to 2021.
White House and U.S. intelligence officials had no comment on whether they believe the so-called Dedicated Denial of Services attacks on the websites of two large Ukrainian banks and the country’s defense ministry and Army were the work of state-sponsored Russian cyber warriors.
Such cyber ops are notoriously hard to attribute, especially given that nation states like Russia often use proxy criminal hacking groups to do their bidding, according to Niemeyer and other current and former U.S. cybersecurity officials.
More: Local governments are more vulnerable to cyberattacks than ever before. DHS wants mayors to step up.
But Putin, a former KGB officer, has a demonstrated history of using destabilizing cyberattacks – often much more destructive than Tuesday’s – in advance of sending in conventional military forces. That’s what happened in 2008, when low-grade attacks against Georgia’s Internet infrastructure preceded an all-out cyberwar that coincided with Russia’s invasion of its neighbor.
Cybersecurity experts say that marked the first time a known cyberattack coincided with a shooting war.
More: Homeland Security warns that Russia could launch cyberattack against US
Russia’s previous cyberattacks on Ukraine
Since then, the Kremlin also has used cyberattacks as an alternative to conventional warfare when trying to destabilize its enemies and undermine citizens’ confidence in their government and private institutions, experts and current and former U.S. officials say.
That’s especially the case with Ukraine, where Moscow is believed to be behind numerous cyberattacks for nearly a decade. In 2015 and 2016, the Kremlin planted malware in the neighboring country’s electric grid, disrupting power for hundreds of thousands of residents in the dead of winter.
By Wednesday morning, officials with Ukraine’s cybersecurity agency said in a briefing that some of their systems were still recovering from a digital assault that likely came from the sophisticated and well-funded adversary.
“The website of the Ministry of Defence of Ukraine was disconnected from the external network to prevent the spread of cyberattacks. The site is not damaged, its full-fledged work will be restored in the near future,” official Victor Zhora said in tweet posted by Ukraine’s State Service of Special Communications and Information Protection.
And while Ukrainian officials did not blame Russia specifically, the cyber agency tweeted, “We see a trace of foreign intelligence services. There are some similarities between this attack and those of January 14.”
In last month’s massive cyberattack, a warning popped up on numerous Kyiv government websites to “be afraid and expect the worst,” adding to an already tense situation. At the time, U.S. officials said they feared that Russia was preparing to create a false pretext to invade Ukraine if it didn’t get its way through diplomacy.
Whoever was responsible for Tuesday’s takedowns was trying to destabilize Ukraine at the height of its crisis with Russia, another Ukrainian official, Natalia Tkachuk, suggested during the briefing.
“We are witnessing a critical change in the mechanisms and purpose of cyberattacks,” Tkachuk was quoted as saying in the official Twitter feed of the briefing. “Previously, this was to obtain specific information for intelligence purposes or to disable them. Today it is a destabilization, a discrediting of the authorities.”
More: Dam releases, bank failures and poisoned water: Cyber pros warn worst cases are possible
Russian threat looms large
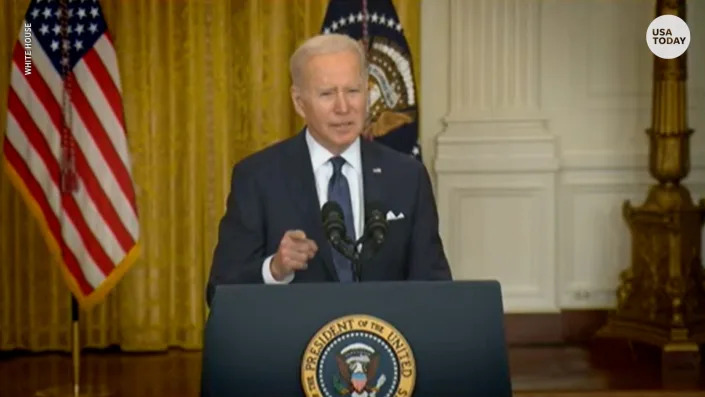
As President Joe Biden said in his Tuesday afternoon address, the looming threat of a full-scale Russian military invasion of Ukraine remains a very real possibility. “And if Russia attacks the United States or our allies through asymmetric means, like disruptive cyberattacks against our companies or critical infrastructure, we are prepared to respond,” he said.
“We’re moving in lockstep with our NATO Allies and partners to deepen our collective defense against threats in cyberspace,” Biden added.
Most cybersecurity experts and current and former U.S. officials interviewed by USA TODAY say Russia is unlikely to directly attack U.S. critical infrastructure, given the threat of countermeasures by Washington.
But it could launch a stealth cyberattack, perhaps through third-party hackers, as retaliation for the Biden administration’s hard line against any attack on Ukraine – and then deny that it played any role in it.
Former top U.S. officials from the White House, Pentagon and National Security Agency warned of just such a scenario in 2014, when Russia was enraged by the Obama administration’s sanctions over its aggressiveness toward Ukraine.
What’s far more likely, they say, is that such cyber weapons will be unleashed on targets in Ukraine.
Cloaking Russian cyberattacks
In some previous cyberattacks on Ukraine, including NotPetya, Russia has hidden extremely powerful “wiper” viruses that can delete entire networks in the form of far more routine-looking malware intrusions and ransomware attempts, Niemeyer said.
“They’ve got some of the best engineers in the world working on that perfect attack that can cloak itself and move laterally” from one computer network to another, said Niemeyer, CEO of Building Cyber Security, a non-profit international cybersecurity organization.
That’s just what happened in June 2017, when Russia’s military cyber-warfare specialists at its military intelligence agency, known as the GRU, targeted government agencies, banks and private companies doing business in Ukraine in an effort to destabilize them and undermine confidence, current and former U.S. officials say.
But the virus, later dubbed NotPetya, jumped the tracks and caused over $10 billion in damage worldwide in what has been described as the most destructive cyberattack ever. As many as 2,000 systems were affected, including the operations of some of the biggest multinational corporations in Europe and North America.
Danish shipping behemoth A.P. Moller-Maersk, the world’s biggest overseas cargo carrier, and even Russia’s own oil giant, Rosneft, were hit.
More: The next big cyberthreat isn’t ransomware. It’s killware. And it’s just as bad as it sounds.
One international pharmaceutical company, Merck, suffered $1.5 billion in U.S. damages in the NotPetya attack, even though its business was far removed from anything to do with Ukraine.
So far, there is no evidence that Russia is preparing to mount destructive cyberattacks even as it continues to negotiate a potential pullback of its forces from attack positions along the border with Ukraine.
More: Congress has tough words on Putin and Russia’s aggression in Ukraine but can’t agree on sanctions
But U.S. officials confirmed that they were on edge, and monitoring the situation for any developments. That includes intentional efforts by Russia to target U.S. critical infrastructure, and the spillover of cyberattacks on Ukrainian targets.
“We’ve known for years that Russia presages its military activities by conducting cyber operations in targeted countries,” said Sen. Mark Warner, D-Va., chairman of the Senate Intelligence Committee. “While these cyber attacks (Tuesday) are not destructive in nature, I worry that Russia could soon escalate, which could lead to spillover effects into American or NATO entities, like the NotPetya attack did in 2017.”
A ‘Shields Up’ warning from US
In recent days, the Department of Homeland Security has been warning local, state and federal law enforcement and government officials – and private sector leaders – to be on high alert for the possibility of cyberattacks in connection with a possible Russian invasion of Ukraine.
“Notably, the Russian government has used cyber as a key component of their force projection over the last decade, including previously in Ukraine in the 2015 timeframe,” DHS’s Cybersecurity and Infrastructure Security Agency said in a “Shields Up” warning. “The Russian government understands that disabling or destroying critical infrastructure – including power and communications – can augment pressure on a country’s government, military and population and accelerate their acceding to Russian objectives.”
“While there are not currently any specific credible threats to the U.S. homeland,” the agency added, “we are mindful of the potential for the Russian government to consider escalating its destabilizing actions in ways that may impact others outside of Ukraine.”

A Department of Homeland Security official confirmed to USA TODAY that top DHS cybersecurity official Jen Easterly spearheaded that effort, trying to raise awareness of the potential for Americans to get caught in the cyber-crossfire that could come with an escalation of hostilities.
Easterly, the director of DHS’s Cybersecurity and Infrastructure Security Agency, also took to Twitter on Saturday to urge U.S. officials to be especially vigilant about possible spillover – and intentional – hacks of critical U.S. infrastructure.
“Every organization in the US is at risk from cyber threats that can disrupt essential services,” Easterly warned in the tweet that included a link for CISA’s “Shields Up” campaign.
Easterly and other federal cybersecurity officials also urged local authorities to significantly lower their threshold for reporting any suspicious activity on their networks, especially power grids and other elements of critical infrastructure that could be especially damaged by a cyber-takedown.
“While there are no specific credible threats to the US homeland at this time, we are mindful of the potential for Russia to consider escalating its destabilizing actions in ways that may affect our critical infrastructure, to include cascading impacts as we saw w/NotPetya,” Easterly wrote. “ALL organizations must adopt a heightened posture of vigilance. The time to act is NOW.”
Russia could also launch a damaging cyberattack against Ukraine even if it ultimately backs down from a military invasion, said retired Army Lt. Col. Alexander Vindman, the former director for Eastern Europe, the Caucasus, and Russia on the White House’s National Security Council during the Trump administration.
Gaming out what Russia has planned
Because such a cyber attack is usually considered “below the threshold of armed conflict,” Russia might view it as a way to continue to undermine the stability of its neighbor without triggering sanctions or other strong reactions from Washington and its NATO allies, said Vindman, who also served as the political-military affairs officer for Russia for the chairman of the Joint Chiefs of Staff and as an attaché at the U.S. Embassy in Moscow.

“I don’t have any evidence to say that one is coming. But it falls completely within the bounds of the way the Russians would operate in this kind of situation,” he said. “The problem with these types of things, with cyber weapons, is that there are no borders. So a spillover effect on the U.S. is not just possible, it’s likely.”
Former U.S. cybersecurity and national security officials differ as to what Russia might do next – if anything.
More: The next big cyberthreat is something called killware
Brian Murphy, a former top Homeland Security and FBI official, said a possible spillover scenario remains a serious threat.
“The Russians remain reckless and once they take action in cyberspace they lose control of the outcome,” said Murphy, who retired last year after serving as acting undersecretary for Intelligence at the Department of Homeland Security. “Putin will continue to meddle in Ukraine and his hybrid warfare techniques will know no boundaries.”
But Chris Krebs, who was Easterly’s predecessor as director of CISA, said he didn’t believe Tuesday’s cyber attack in Ukraine should immediately be seen as a prelude for a Russian invasion.
“If this was an attack on a random government not involved in a geo-political crisis, I wouldn’t think much of it,” Krebs said. “But the fact that it coincides with a country facing the long specter of war, I think it bears further examination.”
Krebs said Russian hackers could target key U.S. government agencies, including the State and Treasury departments to probe for information about the promised U.S. sanctioning strategy in the event of an invasion.
“It is still not clear what Putin is going to do,” Krebs said. “But we do know from events of the past that the Russian intelligence services have a range of capabilities.”
For American business, Krebs said, officials should be preparing for the prospect that “something could happen.”
“You have to take this seriously; you have to prepare.”